Smart Keys with Access Control features
CyberLock is the next generation in access control that secures, controls and audits all assets, from the front door to remote locations

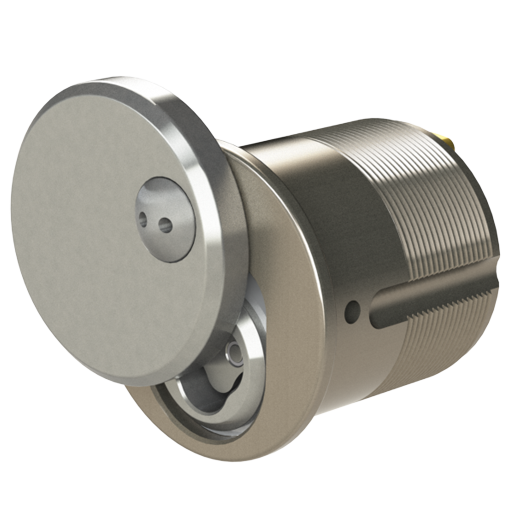
CyberLock is an electro-mechanical master key system. It is a hybrid product that has combined the attributes of conventional proximity or swipe card access control with those of a mechanical master key system. With a CyberLock system, it does not matter where the lock is – electronic access control is possible.
CyberKey is an electronically programmed key that can access a wide range of locks during a designated schedule, with no limit to the quantity or design of locks the key can open. The key’s schedule may also contain an expiration point to completely disable the key until it is audited and reprogrammed.
Smart Key Features



How it works…. Each CyberKey is programmable, meaning the key can only access locks when permissions are granted by a system administrator. Easy to use software and Apps allow keys to be electronically assigned to staff and contractors, either on a permanent basis or by ‘issue and return’. A system administrator can simply select what locks the user can access and when. Once the key is updated it will be able to access the locks at the given date and time. If the keyholder attempts to access locks outside the permitted time frame, the key will be denied entry and the event ‘logged’.
Both locks and keys record audit trail activity for both authorised and denied events. This allows management to track and report on access to every lock, whether that is a door, cabinet or padlock on a gate.
- Programmable Keys; control who, where and when
- Accountability; full audit trail of key holder activity
- No Wiring; install locks with ease, no cables or power
- Intelligent Key; memory, real-time clock and wireless
- Key Communication; Micro USB, Bluetooth and Wifi
