CyberLock communication devices serve as the interface between CyberLock hardware and CyberAudit management software. Access privileges are distributed to key holders via communicators. These devices are linked to the software over a local area network or securely over the Internet. When a CyberKey and communicator make contact, the audit trail is downloaded from the key while simultaneously new schedules, permissions, and system information are uploaded to the key. To increase security and accountability, access privileges can be programmed to expire at scheduled intervals. This results in users regularly updating and reauthorizing keys at communicators.
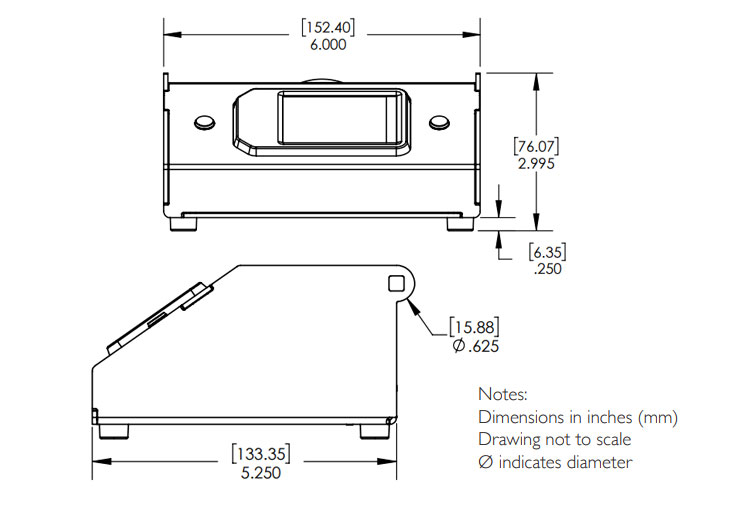
CKV-V02
ValidiKey 2 Vault
The ValidiKey Vault is ideal for shared Keys in an office or department environment. It is matched with the power and flexibility of the CK-Plus Generation 2 Keys. Two Keys may be stored safely and securely in the Vault. When an authorised person needs a Key, they simply swipe their ID card or enter their Job Number (and a PIN if required) and the Vault configures and releases a Keythat is uniquely tailored for them. With both LAN and WiFi connections, it is easily implemented and managed. More significantly, it retains a knowledge of authorised configurations so that it will contimnue to operate even if the link to the software is temporarily lost. With an identical footprint to the ValidiKey Station (CKS-V02), the Station may be mounted on a desk or fixed to a wall.
Communicator Features
- Key activity downloads and key permission updates occur simultaneously.
- Communicator compatibility depends on the key type and version of CyberAudit software installed.
- Several communicators offer multiple functions, such as charging the key battery or storing unprogrammed keys.
- Available with Wiegand compatible card readers