Catalogue Ref: AK-01
Home » Products » Communicators »
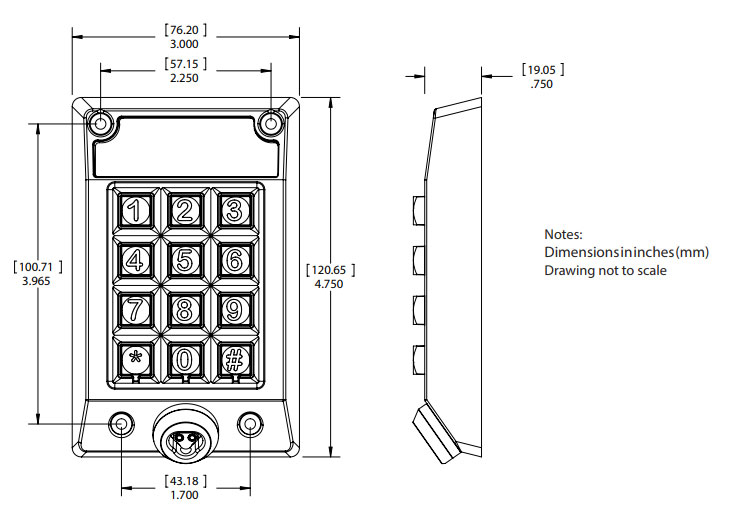
Communicator, indoor/outdoor installation
The is a highly versatile Keypad with the facility to update CyberKeys, but also check they are being used by the correct person (with PIN cotrol activated where this is essential). In addition, the AK-01 allows shared Keys to be activated with a Job Number, making it ideal for contractor control.

The AK-01 keyport is a wall-mounted device that connects directly to the Authorizer Hub. It is a user interface device that includes a keypad and a CyberKey port. The keypad allows for use of PINs for greater security. It can be installed in remote areas without a computer (inside or out) such as a hallway or employee entrance. It is designed to update the full portfolio of Generation 1 CyberKeys.
The KeyPad also allows remote diagnostics such as a check of connection status, battery ID and battery level. Furthermore, the KeyPad Display provides useful feedback to the user of CybnerKeys as well as the Administrator when the system is first configured.

Access privileges are distributed to key holders via communicators. These devices are linked to the software over a local area network or securely over the Internet. When a CyberKey and communicator make contact, the audit trail is downloaded from the key while simultaneously new schedules, permissions, and system information are uploaded to the key.
To increase security and accountability, access privileges can be programmed to expire at scheduled intervals. This results in users regularly updating and reauthorizing keys at communicators.
Specifications